Remove multiple fake Explorer.exe virus (Windows Removal Guide)
Remove multiple fake Explorer.exe virus (Windows Removal Guide)
The real explorer.exe file is a safe Microsoft Windows system process, called “Windows Explorer”. Explorer.exe from Microsoft is an important part of the Windows operating system, however cyber criminals create malware such as viruses, worms, and Trojans deliberately give their processes the same file name to escape detection. Viruses with the same file name are for example TrojanSpy:Win32/SCKeyLog.O or Trojan:Win32/Malagent (detected by Microsoft), and Trojan.Gen or Spyware.SCKeyLogger (detected by Symantec).
Because Explorer.exe it’s part of the operating system, cyber criminals are taking advantage of this process name to hide malware. The explorer.exe file is located in the folder C:\Windows, if explorer.exe is anywhere else then it can be considered malware.
If your computer is very slow and there are multiple instances of Explorer.exe, dllhost.exe or cmmon32.exe process running in Windows Task Manager, then your computer is infected with Trojan.Poweliks. Most often the users who are infected with the Poweliks trojan will see these Explorer.exe process running at Windows start-up (usually more than 6 background process), and while using the computer they will experience very high CPU usage.
What the Explorer.exe Trojan Horse usually does?
Trojans can come in many different varieties, but generally they do the following on your PC:
- Download and install other malware, such as viruses or worms.
- Use your PC for click fraud.
- Record your keystrokes and the sites you visit.
- Send information about your PC to a malicious hacker, including your passwords, login details for websites, and browsing history.
- Give a malicious hacker control over your PC.
How do I know if Explorer.exe is a piece of malware or not?
If your machine is infected with a trojan horse you will see very high CPU usage, and multiple Explorer.exe process running in Task Manager and Windows start-up.
How did Explorer.exe infection got on my computer?
These type of trojans are distributed through several means. Malicious websites, or legitimate websites that have been hacked, can infect your machine through exploit kits that use vulnerabilities on your computer to install this Trojan without your permission of knowledge.
Another method used to propagate this type of malware is spam email containing infected attachments or links to malicious websites. Cyber-criminals spam out an email, with forged header information, tricking you into believing that it is from a shipping company like DHL or FedEx. The email tells you that they tried to deliver a package to you, but failed for some reason. Sometimes the emails claim to be notifications of a shipment you have made. Either way, you can’t resist being curious as to what the email is referring to – and open the attached file (or click on a link embedded inside the email). And with that, your computer is infected with the Explorer.exe virus.
The threat may also be downloaded manually by tricking the user into thinking they are installing a useful piece of software, for instance a bogus update for Adobe Flash Player or another piece of software.
How to remove Explorer.exe malware (Virus Removal Guide)
To remove Explorer.exe virus, follow these steps:
- STEP 1: Scan your computer with ESET Poweliks Cleaner
- STEP 2: Use Rkill to stop the malicious process
- STEP 3: Scan your computer with Malwarebytes Anti-Malware
- STEP 4: Scan your computer with HitmanPro
- (OPTIONAL) STEP 5: Scan your computer with Zemana AntiMalware
STEP 1: Scan your computer with ESET Poweliks Cleaner
In this first step, we will run a system scan with ESET Poweliks Cleaner to remove Trojan.Poweliks that might be installed on your system.
- Poweliks will change your Internet Explorer security settings so that you are unable to download files with it. To fix this, press the Windows key (Windows Key) on your keyboard, and while holding it down, also press the R key on your keyboard. This will open the Run dialog box as shown below.
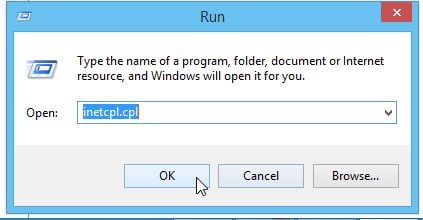
Next, we will need to type inetcpl.cpl in the “Run” box to open the Internet Explorer settings. - In Internet Explorer, click on the “Security” tab, then on “Reset all zones to default level” button. Click on “Apply” and “OK” to save these settings.

- Next, we will need to download ESET Poweliks Cleaner from the below link:
ESET POWELINKS CLEANER DOWNLOAD LINK (This link will download ESET Poweliks Cleaner on your computer) - Once the ESET Poweliks Cleaner tool has been downloaded, look for the file called ESETPoweliksCleaner.exe on your desktop and double-click it.
- You will now be shown the main screen for the ESET Poweliks Cleaner and it will begin to search for the infection. If the tool detects Poweliks, it will state that it found it and then ask if you wish to remove it.

If Poweliks is detected, then press the Y button on your keyboard. ESET Poweliks Cleaner will now remove the Poweliks trojan from your computer.
STEP 2: Use Rkill to stop the malicious process
RKill is a program that will attempt to terminate all malicious processes associated with this infection, so that we will be able to perform the next step without being interrupted by this malicious software.
Because this utility will only stop the malicious process and does not delete any files, after running it you should not reboot your computer.
- You can download Rkill from the below link.
RKILL DOWNLOAD LINK (his link will open a new web page from where you can download “RKill”) - Double click on Rkill program to stop the malicious programs from running.

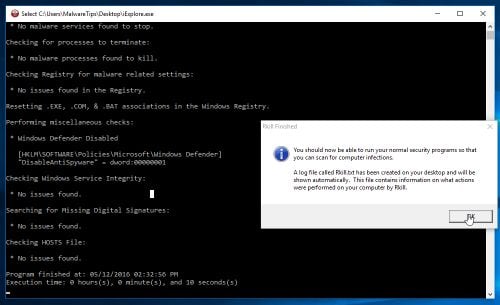
- RKill will now start working in the background, please be patient while this utiltiy looks for malicious process and tries to end them.
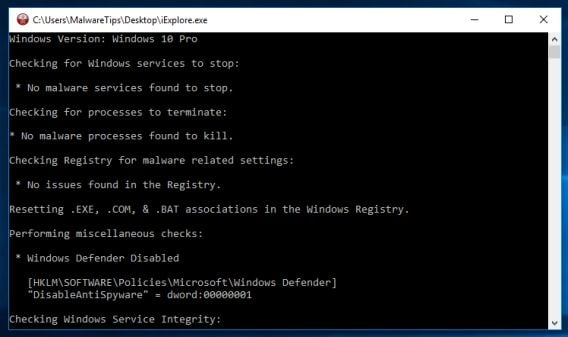
- When the Rkill tool has completed its task, it will generate a log. Do not reboot your computer after running RKill as the malware programs will start again.
STEP 3: Scan your computer with Malwarebytes Anti-Malware
Malwarebytes Anti-Malware is a powerful on-demand scanner which should remove the dllhost.exe *32 COM malware from your machine. It is important to note that Malwarebytes Anti-Malware will run alongside antivirus software without conflicts.
- You can download download Malwarebytes Anti-Malware from the below link.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a new web page from where you can download “Malwarebytes Anti-Malware”) - Once downloaded, close all programs, then double-click on the icon on your desktop named “mbam-setup” to start the installation of Malwarebytes Anti-Malware.

You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- When the installation begins, you will see the Malwarebytes Anti-Malware Setup Wizard which will guide you through the installation process.

To install Malwarebytes Anti-Malware on your machine, keep following the prompts by clicking the “Next” button.
- Once installed, Malwarebytes Anti-Malware will automatically start and will update the antivirus database. To start a system scan you can click on the “Scan Now” button.

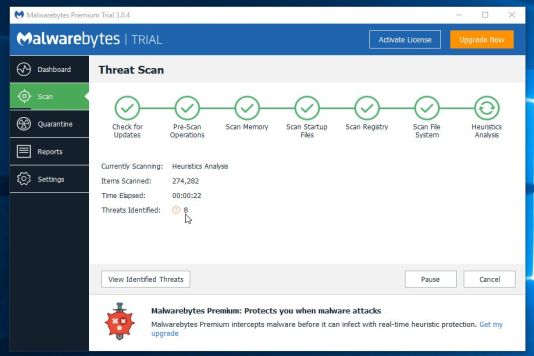
- Malwarebytes Anti-Malware will now start scanning your computer for malware. When Malwarebytes Anti-Malware is scanning it will look like the image below.
- When the scan has completed, you will be presented with a screen showing the malware infections that Malwarebytes Anti-Malware has detected. To remove the malicious programs that Malwarebytes Anti-malware has found, click on the “Remove Selected” button.
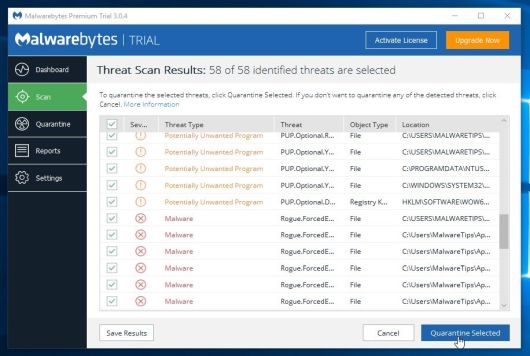
- Malwarebytes Anti-Malware will now quarantine all the malicious files and registry keys that it has found. When removing the files, Malwarebytes Anti-Malware may require a reboot in order to remove some of them. If it displays a message stating that it needs to reboot your computer, please allow it to do so.
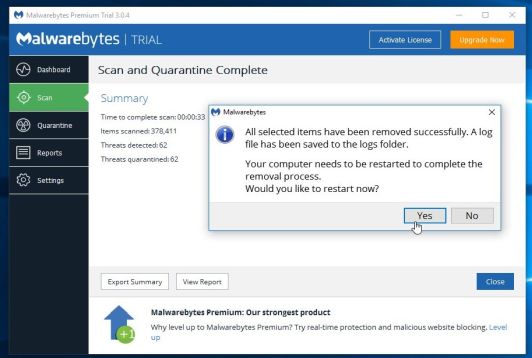
After your computer will restart, you should open Malwarebytes Anti-Malware and perform another scan to verify that there are no remaining threats
STEP 4: Scan your computer with HitmanPro
HitmanPro can find and remove malware, adware, bots, and other threats that even the best antivirus suite can oftentimes miss. HitmanPro is designed to run alongside your antivirus suite, firewall, and other security tools.
- You can download HitmanPro from the below link:
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download “HitmanPro”) - Double-click on the file named “HitmanPro.exe” (for 32-bit versions of Windows) or “HitmanPro_x64.exe” (for 64-bit versions of Windows).

Click on the “Next” button, to install HitmanPro on your computer.
- HitmanPro will now begin to scan your computer for malware.
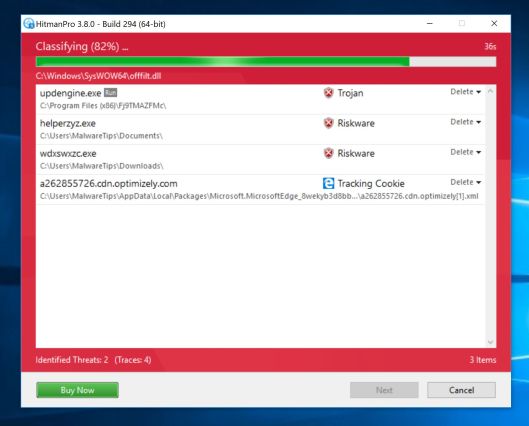
- When it has finished it will display a list of all the malware that the program found as shown in the image below. Click on the “Next” button, to remove malware.
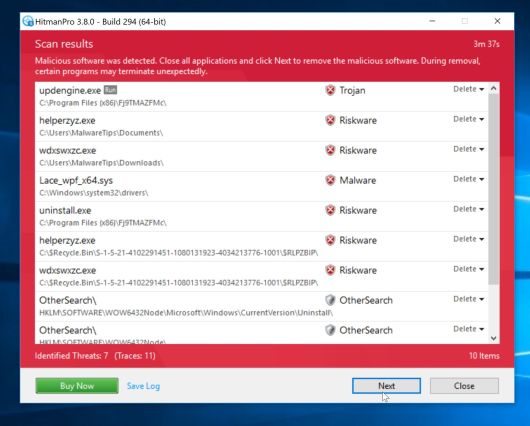
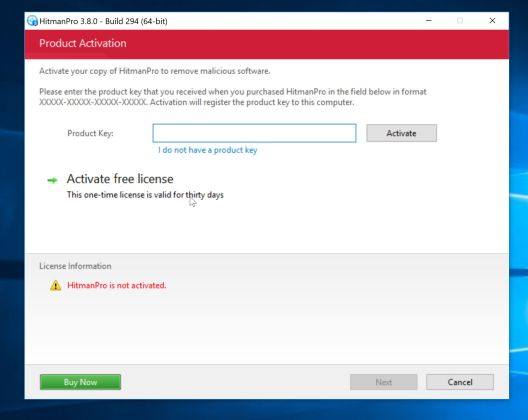
- Click on the “Activate free license” button to begin the free 30 days trial, and remove all the malicious files from your computer.
(OPTIONAL) STEP 5: Scan your computer with Zemana AntiMalware
Zemana AntiMalware is a powerful utility which will remove Explorer.exe malware from your machine.
This step should be performed only if your issues have not been solved by the previous steps.
This step should be performed only if your issues have not been solved by the previous steps.
- You can download Zemana AntiMalware from the below link:
ZEMANA ANTIMALWARE DOWNLOAD LINK (This link will start the download of “Zemana AntiMalware”) - Double-click on the file named “Zemana.AntiMalware.Setup.exe” to start the installation of Zemana AntiMalware.
You may be presented with a User Account Control dialog asking you if you want to run this file. If this happens, you should click “Yes” to continue with the installation.
- Click on the “Next” button, to install Zemana AntiMalware on your computer.

- When Zemana AntiMalware will start, click on the “Scan” button.
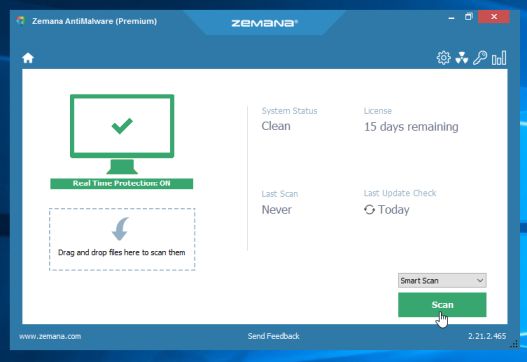
- Zemana AntiMalware will now scan computer for malicious files. This process can take up to 10 minutes.
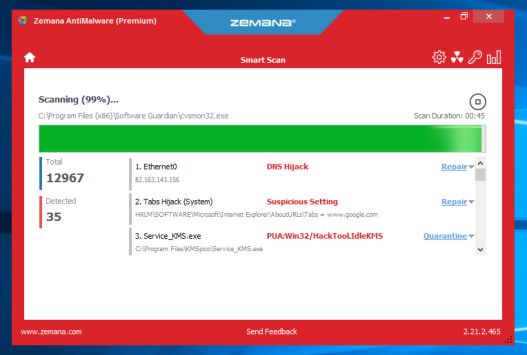
- When Zemana AntiMalware has finished it will display a list of all the malware that the program found. Click on the “Next” button, to remove the malicious files from your computer.
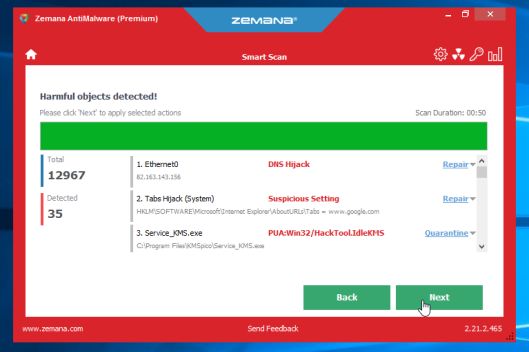
Zemana AntiMalware will now remove all the detected malicious files, and at the end a system reboot may be required to remove all traces of malware.
ReplyDeleteI guess I am the only one who came here to share my very own experience. Guess what!? I am using my laptop for almost the past 2 year! but I had no idea of solving some basic issues. I do not know how to fullcrackedpc.com But thankfully, I recently visited a website named vsthomes.com
licenselinks.info
HitmanPro Crack
Tomabo MP4 Downloader Pro crack
MEmu Android Emulator crack
Thanks for sharing, if you want more benefits then remain connect with us.
ReplyDeleteMalwarebytes Anti-Malware Crack
Hey there, I really appreciate that you have taken out some time to share this information. I have fully understood about each and every point that you shared here.
ReplyDeletewebsite malware scanner
magoshare-data-recovery-crack
ReplyDeleteVery good article! We will be linking to this particularly great post on our website. Keep up the good writing.
ReplyDeleteHitmanPro Crack
SideFX Houdini FX Crack
Serato DJ Pro Crack
Thanks for sharing your knowledge to install & crack the Time Tables, but you need to update
ReplyDeleteit now. because there is a 2022 version available now:
portablecrack.co
zemana-antimalware-premium-crack
ispring-suite
nitro-pro
ReplyDeleteJust admiring your work and wondering how you managed this blog so well. It’s so remarkable that I can't afford to not go through this valuable information whenever I surf the internet! android emulators
zemana-antimalware-torrent-crack
auslogics-boostspeed-premium-crack
golden-software-grapher-crack
allegorithmic-substance-designer-crack
pdf-xchange-editor-crack
whatsender-pro-crack
auto-macro-recorder-crack
wps-office-crack-apk
nuclear-coffee-videoget-crack
nuclear-coffee-videoget-crack
aomei-onekey-recovery-professional-crack
renee-passnow-pro-crack
Such a Nice post. Thanks for Awesome tips Keep it up
ReplyDeleteZemana Antimalware Crack
Smith Micro Moho Pro Crack
XMind Pro Crack
ABBYY FineReader Corporate Crack